Table of Contents What is the New Remote Reality in 2025?Advanced Remote Work Security StrategiesEmbrace Zero Trust ArchitectureDeploy Endpoint Detection and Response (EDR) SolutionsStrengthen Secure Access wi...
Table of Contents Why Should Small Businesses Consider the Right Cloud Storage?Choosing the Right Cloud Storage for Your Small BusinessKnow Your Storage NeedsEvaluate Your BudgetPrioritize Security and Complia...
Table of Contents Why Is Cyber Insurance More Crucial Than Ever?What Cyber Insurance Typically CoversFirst-Party CoverageBreach Response CostsBusiness InterruptionCyber Extortion and RansomwareData Restoration...
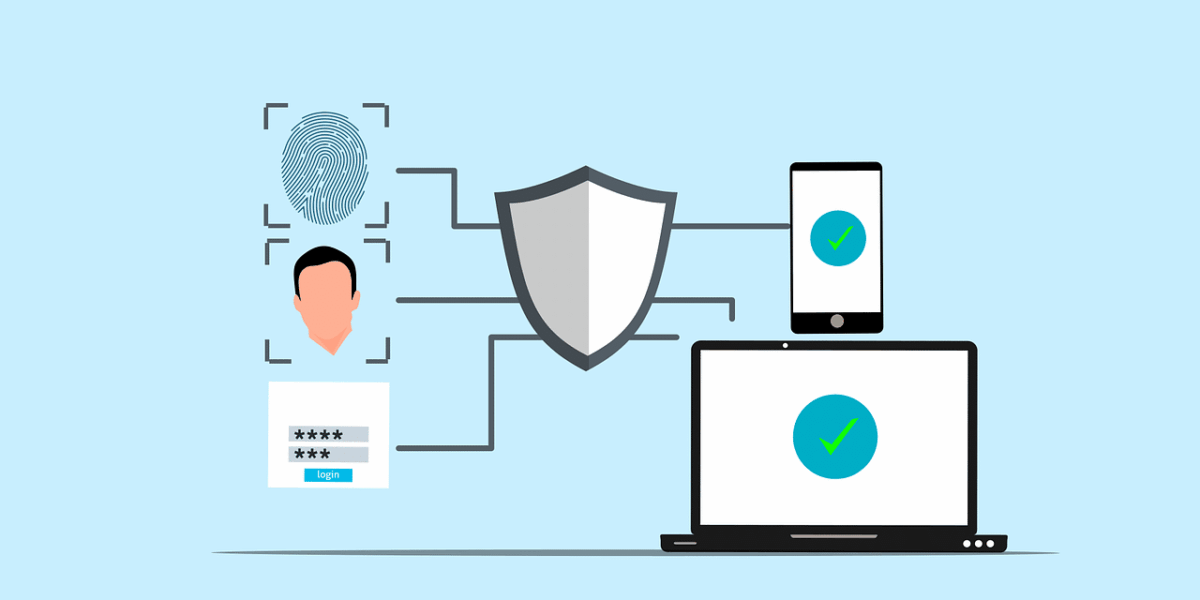
Table of Contents Why is Multi-Factor Authentication Crucial for Small Businesses?What is Multi-Factor Authentication?Something You KnowSomething You HaveSomething You AreHow to Implement Multi-Factor Authenti...
Table of Contents Why Does AI-Powered Automation Matter for Small Businesses?Smart Ways to Automate Daily Tasks and Free Up Your Time (Without a Huge Budget)1. Automate Customer Support Without Losing the Pers...
Table of Contents What is the Dark Web and How Does It Work?Can Data Be Removed from the Dark Web?Understanding The Challenges of Data RemovalProactive Measures for ProtectionHow Can I Enhance My Digital Secur...
Table of Contents What Are the Most Common Hacking Techniques?How Do Hackers Exploit Lesser-Known Vulnerabilities?Cookie HijackingSIM SwappingDeepfake TechnologyExploiting Third-Party AppsPort-Out FraudKeylogg...
Table of Contents What Is Data Collection On Websites?How Does Data Sharing Work?Understanding Data Sharing MethodsChallenges In Data SharingHow Should Websites Manage User Data?Best Practices for Data Managem...
Table of Contents What is Cloud Storage and How Does It Work?How Do You Choose a Secure Cloud Storage Provider?Key Features to Look for in a Secure ProviderHow Can You Enhance Cloud Storage Security?Implementi...
Table of Contents Why Are Strong Passwords Essential?How Does Multi-Factor Authentication Enhance Security?Types of Authentication FactorsCommon MFA MethodsWhat Are the Latest Trends in Authentication?How Can ...